Install Proprietary NVIDIA Driver On Kali Linux – NVIDIA Accelerated Linux Graphics Driver
This guide explains how to install proprietary “NVIDIA Accelerated Linux Graphics Driver” or NVIDIA driver on Kali Linux system. If you are using Kali Linux and have NVIDIA graphics card then most likely you are using open source NVIDIA driver nouveau. You can see it by lsmod | grep nouveau command. nouveaudriver works quite well, but if you want to use 3D acceleration feature or want to use GPU based applications (such as CUDA and GPU pass through) then you need to install proprietary NVIDIA driver. The proprietary “NVIDIA Accelerated Linux Graphics Driver” provides optimized hardware acceleration of OpenGL applications via a direct-rendering X server. It is a binary-only Xorg driver requiring a Linux kernel module for its use. The first step is to fully update your Kali Linux system and make sure you have the kernel headers installed.
Where you had to download NVIDIA Driver (CUDA) manually and edit grub.cfg file to make everything work. Because it will be a long guide, I had to divide it into two parts:
You use the first guide to install NVIDIA Driver. If you want GPU acceleration, (cudahashcat, GPU pass through etc.) keep reading and follow the second guide to complete your installation. I’ve included as much details I can, including troubleshooting steps and checks but I would like to hear your part of the story, so leave a comment with your findings and issues.
The new NVIDIA Driver
The new Linux binary NVIDIA drivers nvidia-kernel-dkms builds the NVIDIA Xorg binary kernel module needed by NVIDIA driver, using DKMS. Provided that you have the kernel header packages installed, the kernel module will be built for your running kernel and automatically rebuilt for any new kernel headers that are installed. The binary NVIDIA drivers provide optimized hardware acceleration of OpenGL applications via a direct-rendering X Server for graphics cards using NVIDIA chip sets. AGP, PCIe, SLI, TV-out and flat panel displays are also supported. NVIDIA Added support for the following GPU including fixing some issues: (existing GPU’s are already supported).
- GeForce GT 710
- GeForce 825M
- Fixed a regression that prevented NVIDIA-installer from cleaning up directories created as part of the driver installation.
- Added a new X configuration option “InbandStereoSignaling” to enable/disable DisplayPort in-band stereo signaling.
- Fixed a bug that caused PBO downloads of cube map faces to retrieve incorrect data.
- Fixed a bug in NVIDIA-installer that resulted in spurious error messages when opting out of installing the NVIDIA kernel module or source files for the kernel module.
- Added experimental support for ARGB GLX visuals when Xinerama and Composite are enabled at the same time on X.Org xserver 1.15.
See the details about this driver in NVIDIA official website:
Debian Linux usually ports that Official Driver to fit it’s requirements. The NVIDIA driver graphics processing unit (GPU) series/codename of an installed video card can usually be identified using the lspci command. For example:
lspci -nn | grep VGA
My settings
My PC got the following configuration:

I’ve installed everything in a brand new Kali Linux 1.0.6 installation, fully updated and upgraded. Before you do anything, you of course add the Official Kali Linux repository. Once I’ve added the correct Kali Official repositories, I’ve issued the following commands to update, upgrade and dist-upgrade my Kali Linux.
apt-get update && apt-get upgrade -y && apt-get dist-upgrade -y
If you’ve completed this part, move on to the next instruction.
Step 1: Install Linux headers
Install Linux headers as those will be required to build NVIDIA Driver modules.
aptitude -r install linux-headers-$(uname -r)
Where -r means install all recommended packages as well. 
Step 2: Install NVIDIA Kernel
Next I installed NVIDIA Kernel
apt-get install nvidia-kernel-$(uname -r)

Step 3: Install NVIDIA Driver Kernel DKMS
We’re almost ready. You can now install new NVIDIA driver nvidia-kernel-dkms by using the following command:
aptitude install nvidia-kernel-dkms

Including dependencies, this is about 24MB is size, depending on how fast Kali repo is working, you might have to wait few minutes. You will get 2 popups, the first one about rebooting after you’ve installed NVIDIA drivernvidia-kernel-dkms that it will disable open source NVIDIA driver nouveau and the second one about xorg.conf file in /etc/X11/ folder.

Press OK on both popups.
Step 4: Install xconfig NVIDIA driver application
If you go through the NVIDIA driver README document, you will see you need to create new XORG server configuration file xorg.conf or modify existing xorg.conf to tell it to load NVIDIA Driver module.nvidia-xconfig package make this task quite easier. All you need to do is to install and execute it.
aptitude install nvidia-xconfig

Step 5: Generate Xorg server configuration file
Now that we have installed nvidia-xconfig package, issue the following command to generate Xorg server configuration file.
nvidia-xconfig

It will rename any existing xorg.conf file and create a new one. As directed by NVIDIA drivernvidia-kernel-dkms, reboot your machine to complete installation.
Step 6: Confirming your installation
At this point you should be able to login to your system in Graphical User Mode (GUI). In case you can’t, follow the troubleshooting section at the bottom of this article. As always, we need to check if everything went as expected.
Step 6.a: Check GLX Module
First check if system is using glx module.
glxinfo | grep -i "direct rendering"
It should output “direct rendering: Yes”

If you do not have glxinfo then first install mesa-utils package then again issue above command and check output
aptitude install mesa-utils
Step 6.b: Check NVIDIA Driver Module
Check if NVIDIA module loaded.
lsmod | grep nvidia

If it produces output like nvidia 9442880 28 or something similar (numbers could be different at your system) then NVIDIA module is loaded.
Step 6.c: Check for Open source NVIDIA Driver nouveau module
Just to be sure Open source NVIDIA Driver nouveau module NOT loaded, issue following command
lsmod | grep nouveau

It should NOT produce any output. If it produces output then something is wrong.
Step 6.d: Confirm if open source NVIDIA Driver nouveau was blacklisted
I like this new NVIDIA Driver. It blacklists Open source NVIDIA Driver nouveau by default. That means less work for us to do. You can confirm it by checking files in the following directory:
cat /etc/modprobe.d/nvidia.conf
cat /etc/modprobe.d/nvidia-blacklists-nouveau.conf
cat /etc/modprobe.d/nvidia-kernel-common.conf
Troubleshooting
You might get a black screen after installing NVIDIA Driver. Following are your options to fix it:
Troubleshooting Step A: Fixing black screen with a cursor problem
Simply press CTRL + ALT + F1 and login. Type the following
nvidia-xconfig
reboot
You should now be able to log in using the GDM3 GUI.
Troubleshooting Step B: Delete xorg.conf file
Press CTRL + ALT + F1 and login. Type the following
rm /etc/X11/xorg.conf
reboot
After reboot, you should be able to log in using the GDM3 GUI.
Troubleshooting Step C: remove NVIDIA Driver
Press CTRL + ALT + F1 and login. Type the following
apt-get remove nvidia-kernel-dkms
reboot
After reboot, you should be able to log in using the GDM3 GUI.
Conclusion
This concludes my general instructions on how to install proprietary NVIDIA driver on Kali Linux – NVIDIA Accelerated Linux Graphics Driver. NVIDIA Optimus users should be able to follow the same instructions, however, as I said before, feel free to share your side of story on how your installation went and correct my guide if required. I am open for discussion and will try to reply back to your comments the earliest possible. For those curious minds, try installing nvidia-settings and see how that goes. NVIDIA Settings will remove NVIDIA Driver but I did manage to make it work with some tinkering. I will try to write another guide on that (NVIDIA Settings presents you with a GUI X Config Window and you can see GPU Temperature and more info)… The proprietary “NVIDIA Accelerated Linux Graphics Driver” provides optimized hardware acceleration of OpenGL applications via a direct-rendering X server, in shoty your NVIDIA Driver give you better display and 3D rendering then you’re all done. You can now play 3D Games. Let me know if you want any specific Linux supported games on Kali and I can write up an article on that. But if you want to run applications that uses NVIDIA Kernel Module CUDA, Pyrit and Cpyrit for GPU processing then you will also need to install CUDA drivers, replace offical Pyrit and install Cpyrit. Find out if your Graphics Card supports CUDA in the following page from NVIDIA
Mine does,
Next guide will show you how to Install NVIDIA Kernel Module CUDA and Pyrit in Kali Linux – CUDA, pyrit and cpyrit. Thanks for reading. If this guide helped you to install NVIDIA Driver, please share this article and follow us in Facebook/Twitter.
Install NVIDIA driver kernel Module CUDA and Pyrit on Kali Linux – CUDA, Pyrit and Cpyrit-cuda
In this guide, I will show how to install NVIDIA driver kernel Module CUDA, replace stock Pyrit, and install Cpyrit.At the end of this guide, you will be able to use GPU acceleration for enabled applications such as cudaHashcat, Pyrit, crunch etc.
You use the first guide to install NVIDIA Driver on Kali Linux. I would assume you followed the first guide and completed all steps there and would like to enable GPU acceleration, (cudahashcat, GPU pass through etc.) on your Kali Linux.
CUDA Toolkit
The NVIDIA® CUDA® Toolkit provides a comprehensive development environment for C and C++ developers building GPU-accelerated applications. The CUDA Toolkit includes a compiler for NVIDIA GPUs, math libraries, and tools for debugging and optimizing the performance of your applications. You’ll also find programming guides, user manuals, API reference, and other documentation to help you get started quickly accelerating your application with GPUs. You can read a lot more here in NVIDIA Developers official webpage:
CUDA Toolkit
Prerequisites
Following are the prerequisite before you start following this guide:
Prerequisite 1: add Official Kali Linux repository.
I’ve added the correct Kali Official repositories and issued the following commands to update, upgrade and dist-upgrade my Kali Linux.
apt-get update && apt-get upgrade -y && apt-get dist-upgrade -y
Prerequisite 2: Install proprietary NVIDIA driver on Kali Linux
I’ve installed the correct official proprietary NVIDIA driver on Kali Linux – NVIDIA Accelerated Linux Graphics Driver using the previous guide.
If you’ve completed both, move to next instruction.
Step 1: Install NVIDIA CUDA toolkit and openCL
At first we need to install NVIDIA CUDA toolkit and NVIDIA openCL
aptitude install nvidia-cuda-toolkit nvidia-opencl-icd

This will install CUDA packages in your Kali Linux. The total package is pretty large including dependencies, (282MB something), you be patient and let it finish.
Step 2: Download Pyrit and Cpyrit
Download Pyrit and Cpyrit from the official website:
http://pyrit.googlecode.com

Save them in your /root folder.
Step 3: Install Pyrit
Follow the instructions below to install Pyrit and it’s prerequisites.
Step 3.a: Install Pyrit prerequisites
apt-get install python2.7-dev python2.7-libpcap libpcap-dev

Step 3.b: Remove existing installation of Pyrit
Remove stock Pyrit using the following command:

You get a message stating that it will also remove kali-linux-full package. It actually doesn’t. All it does updating Kali repo and remove Pyrit. Finish removing Pyrit.
If you are not using a clean install of Kali (not recommended), you may need to issue the following command:
rm -r /usr/local/lib/python2.7/dist-packages/cpyrit/
Step 3.c: Install new Pyrit
Copy paste the following commands to extract downloaded Pyrit in your Kali Linux /root directory
tar -xzf pyrit-0.4.0.tar.gz
cd pyrit-0.4.0

Now build the package
python setup.py build
Once build is complete, you can install Pyrit.
python setup.py install

Up to this point, you shouldn’t receive any errors.
Step 4: Install CPyrit-cuda
Copy paste the following commands to extract downloaded CPyrit-cuda in your Kali Linux /root directory
tar -xzf cpyrit-cuda-0.4.0.tar.gz
cd cpyrit-cuda-0.4.0

Now build the package
python setup.py build
Once build is complete, you can install CPyrit-cuda.
python setup.py install

Again, you shouldn’t receive any errors, if there’s error, go back and review each steps.
Step 5: Testing and troubleshooting
Now that we’ve installed NVIDIA driver kernel Module CUDA and Pyrit on Kali Linux, we should be able to test it. The best way to test is by issuing the following command:
pyrit list_cores
This gave me an error “ bash: /usr/bin/pyrit: No such file or directory “.
It seems this Pyrit puts its binaries in wrong folder than you’d expect. The actual path for Pyrit is now/usr/local/bin/pyrit
Step 5.a Softlink them or add path to profile
There’s two different ways you can resolve it. You can either softlink or add this /usr/local/bin/ path to your profile. Choice is again yours.
Step 5.a.i: Softlinking
This is what I’ve followed
ln -s /usr/local/bin/pyrit /usr/bin/pyrit

Step 5.a.ii: Add path
If you want only to specific user edit ~/.bash_profile or ~/.bashrc and put there
export PATH=$PATH:/usr/local/bin
If you want for all users edit /etc/profile and scroll down until you see something like
PATH="/bin:/usr/bin:/sbin:/usr/sbin" export PATH
Append to the end /usr/local/bin. it will be
PATH="/bin:/usr/bin:/sbin:/usr/sbin:/usr/local/bin"
and Finally
Once you’ve either Softlinked or added the correct path to your profile, then following is what you get
root@kali:~# pyrit list_cores
Pyrit 0.4.0 (C) 2008-2011 Lukas Lueg http://pyrit.googlecode.com
This code is distributed under the GNU General Public License v3+
The following cores seem available...
#1: 'CUDA-Device #1 'GeForce 210''
#2: 'CPU-Core (SSE2)'
#3: 'CPU-Core (SSE2)'
#4: 'CPU-Core (SSE2)'
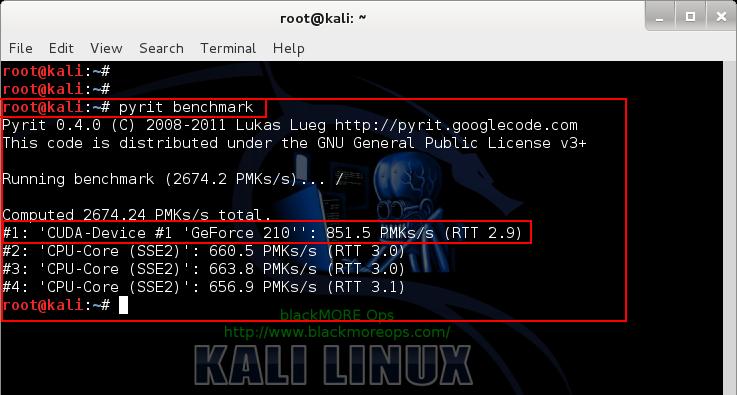
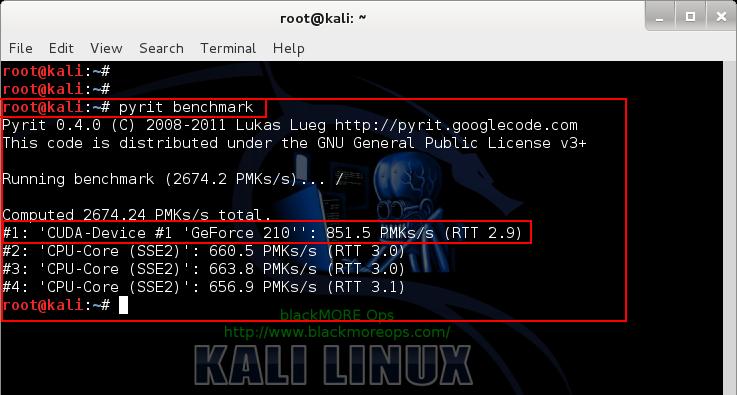
and of course I did a benchmark with my GeForce 210 card:
root@kali:~# pyrit benchmark
Pyrit 0.4.0 (C) 2008-2011 Lukas Lueg http://pyrit.googlecode.com
This code is distributed under the GNU General Public License v3+
Running benchmark (2744.1 PMKs/s)... -
Computed 2744.11 PMKs/s total.
#1: 'CUDA-Device #1 'GeForce 210'': 853.1 PMKs/s (RTT 3.0)
#2: 'CPU-Core (SSE2)': 648.1 PMKs/s (RTT 2.8)
#3: 'CPU-Core (SSE2)': 647.6 PMKs/s (RTT 2.9)
#4: 'CPU-Core (SSE2)': 658.5 PMKs/s (RTT 3.0)
root@kali:~#
Conclusion
Pyrit allows to create massive databases, pre-computing part of the IEEE 802.11 WPA/WPA2-PSKauthentication phase in a space-time-tradeoff. Exploiting the computational power of Many-Core- and other platforms through ATI-Stream, Nvidia CUDA and OpenCL, it is currently by far the most powerful attack against one of the world’s most used security-protocols.
Here’s a great benchmark done with Pyrit and CUDA for different GPU’s

Thanks for reading. If this guide helped you to install NVIDIA driver kernel Module CUDA and Pyrit on Kali Linux – CUDA, Pyrit and Cpyrit-cuda, please share this article and follow me in Facebook/Twitter.
ah and don’t forget to show off your Pyrit Benchmark. ;)